IPsec provides security services through AH and ESP. The two IPsec peers establish security associations for key exchange and security services by the Internet Key Exchange (IKE) protocol. RFC 2409 specifies the Internet Key Exchange Protocol (IKEv1), while RFC 7296 defines the Internet Key Exchange Protocol Version 2 (IKEv2).
Security Associations for Key Exchange
In IKEv1, the ISAKMP SA is two-way or bi-directional:
The ISAKMP SA is bi-directional. That is, once established, either party may initiate Quick Mode, Informational, and New Group Mode Exchanges.
~ RFC 2409
Security Associations for AH and ESP
Both AH and ESP security associations (one-way, either inbound or outbound) are established based on the IKE security association. In IKEv2, SAs established based on IKE SA are called Child SAs.
SA (Security Association): a one-way (inbound or outbound) agreement between two communicating peers that specifies the IPsec protections to be provided to their communications. This includes the specific security protections, cryptographic algorithms, and secret keys to be applied, as well as the specific types of traffic to be protected.
~ RFC 6071
Internet Key Exchange (IKE) Version 1
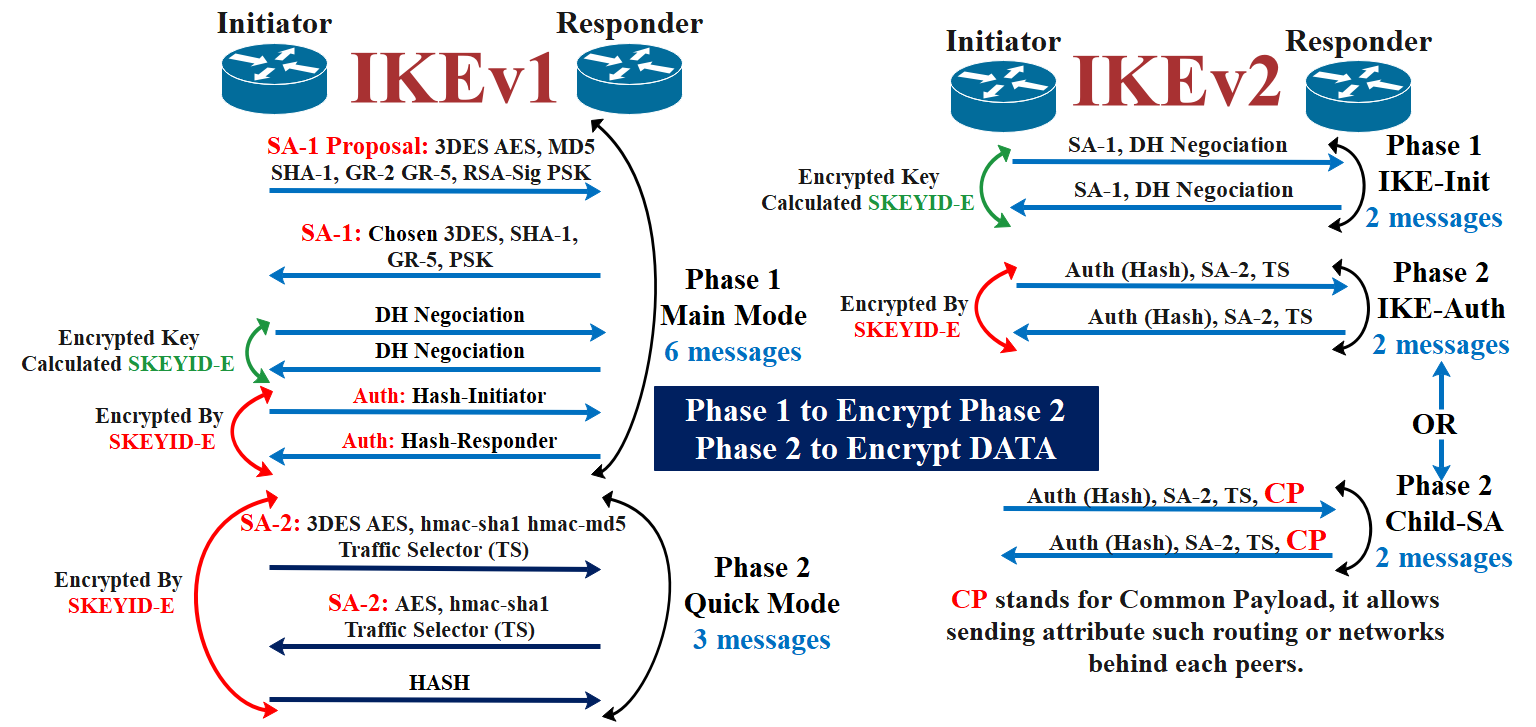
In IKE v1, ISAKMP defines “phases,” while Oakley defines “modes.” Security association negotiation happens in each mode, e.g., Main Mode, Aggressive Mode, and Quick mode.
In phase 1, a bi-directional secure, authenticated channel, aka ISAKMP security association (SA), is established between the two peers. Either “Main Mode” or “Aggressive Mode” is used in phase 1 to do so.
In phase 2, a one-way security association for AH or ESP is established using the “Quick Mode.”
For a successful and secure communication using IPsec, the Internet Key Exchange (IKE) protocols take part in a two-step negotiation. Main mode or Aggressive mode (within Phase 1 negotiation) authenticate and/or encrypt the peers. Quick mode (Phase 2) negotiates the algorithms and agree on which traffic will be sent across the VPN. Let’s take a further look at Quick mode phase (Phase 2) and what it’s role is within an IPsec VPN tunnel.
~ Internet-Computer-Security.com
IKEv1 Phase 1: Main Mode

IKEv1 Phase 2: Quick Mode

