
Your organization sets out an access control policy. You are evaluating access control mechanisms to support it. Which of the following is correct? (Wentz QOTD)
A. Mandatory and discretionary protection are mutually exclusive in a trusted computer system.
B. Bell-Lapadula and Biba models are mutually exclusive in a trusted computer system.
C. Conflict-of-interest classes are mutually exclusive in the Brewer and Nash model.
D. Zero Trust and the castle-and-moat network security model are mutually exclusive.
Kindly be reminded that the suggested answer is for your reference only. It doesn’t matter whether you have the right or wrong answer. What really matters is your reasoning process and justifications.
My suggested answer is C. Conflict-of-interest classes are mutually exclusive in the Brewer and Nash model.
Wentz’s book, The Effective CISSP: Security and Risk Management, helps CISSP and CISM aspirants build a solid conceptual security model. It is a tutorial for information security and a supplement to the official study guides for the CISSP and CISM exams and an informative reference for security professionals.

This model is commonly used by consulting and accounting firms. For example, once a consultant accesses data belonging to Acme Ltd, a consulting client, they may no longer access data to any of Acme’s competitors. In this model, the same consulting firm can have clients that are competing with Acme Ltd while advising Acme Ltd. This model uses the principle of data isolation within each conflict class of data to keep users out of potential conflict of interest situations. Because company relationships change all the time, dynamic and up to date updates to members and definitions for conflict classes are important.
Source: Wikipedia
MAC and DAC
In TCSEC (Orange Book), trusted computer systems compliant with Division C must support DAC, while the ones compliant with Division B must support MAC. A Division B system must meet both the requirements of Division C and Division B. It means DAC and MAC are supported in Division B systems.

Bell-Lapadula and Biba Models
Bell-Lapadula and Biba models are NOT mutually exclusive in a trusted computer system. For example, The Lipner model combines elements of Bell-LaPadula and Biba.
Lipner Model–Lipner combines elements of Bell-LaPadula and Biba together with the idea of job functions or roles in a novel way to protect both confidentiality and integrity. The Lipner implementation, published in 1982, describes two ways of implementing integrity. One uses the Bell-LaPadula confidentiality model, and the other uses both the Bell-LaPadula model and the Biba integrity model together. Both methods assign security levels and functional categories to subjects and objects. For subjects, this translates into a person’s clearance level and job function (e.g., user, operator, applications programmer, or systems programmer). For objects, the sensitivity of the data or program and its functions (e.g, test data, production data, application program, or system program) are defined according to its classification.

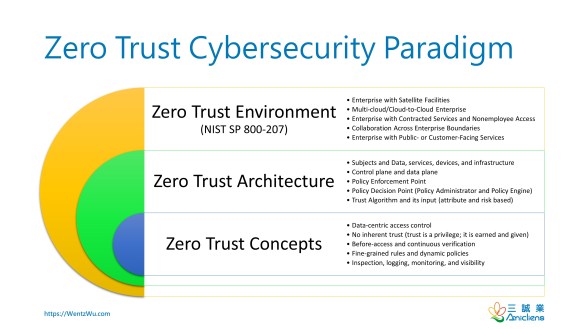
Zero Trust and Castle-and-Moat
Zero Trust doesn’t take the big bang or revolutionary approach. Instead, it takes an evolutionary approach. In other words, a traditional castle-and-moat network can be replaced with zero-trust-based networks gradually.
Reference
您的組織制定了訪問控制政策。 您正在評估訪問控制機制以支持它。 以下哪個是正確的? (Wentz QOTD)
A. 在受信任的計算機系統中,強制保護(MAC)和自主保護(DAC)是相互排斥的。
B. Bell-Lapadula 和 Biba 模型在可信計算機系統中是互斥的。
C. 在 Brewer 和 Nash 模型中,利益衝突類別是相互排斥的。
D. 零信任和城堡護城河網絡安全模型是相互排斥的。
