
Your company decides to build a virtualized data center to provision cloud services as a new business. It is estimated that the financial break-even requires five thousand customers. Which of the following is the best technology to support the new business? (Wentz QOTD)
A. Virtual LAN (VLAN)
B. Private VLAN
C. EAP over LAN
D. Virtual eXtensible Local Area Network (VXLAN)
Kindly be reminded that the suggested answer is for your reference only. It doesn’t matter whether you have the right or wrong answer. What really matters is your reasoning process and justifications.
My suggested answer is D. Virtual eXtensible Local Area Network (VXLAN).
Wentz’s book, The Effective CISSP: Security and Risk Management, helps CISSP and CISM aspirants build a solid conceptual security model. It is a tutorial for information security and a supplement to the official study guides for the CISSP and CISM exams and an informative reference for security professionals.
Virtual LAN (VLAN)

A virtual LAN (VLAN) is any broadcast domain that is partitioned and isolated in a computer network at the data link layer (OSI layer 2).
Source: Wikipedia
The current VLAN has a limited number of 4094, which cannot meet the requirements of data centers or cloud computing with a common feature where networks are isolated based on tenants. For example, Azure or AWS has far more customers than 4094.
Private VLAN

Private VLAN, also known as port isolation, is a technique in computer networking where a VLAN contains switch ports that are restricted such that they can only communicate with a given uplink. The restricted ports are called private ports. Each private VLAN typically contains many private ports, and a single uplink. The uplink will typically be a port (or link aggregation group) connected to a router, firewall, server, provider network, or similar central resource.
A typical application for a private VLAN is a hotel or Ethernet to the home network where each room or apartment has a port for Internet access.
Source: Wikipedia
VXLAN Problem Statement
VXLAN (RFC 7348) is designed to solve this problem. VXLAN problem statement highlights the following issues:
- Limitations Imposed by Spanning Tree and VLAN Ranges
- Multi-tenant Environments
- Inadequate Table Sizes at ToR (Top-of-Rack) Switch
It also reads: “VXLAN (Virtual eXtensible Local Area Network) addresses the above requirements of the Layer 2 and Layer 3 data center network infrastructure in the presence of VMs in a multi-tenant environment.”
VXLAN as Overlay Network
VXLAN encapsulates the traditional VLAN frame as an IP payload or MAC-over-IP to support communication between spine switches and leaf switches. The leaf-spine architecture employs a two-layer network topology composed of leaf switches and spine switches.

Overlay and Underlay Networks
Underlay networks or so-called Physical networks where traditional protocols are working. Underlay Network is physical infrastructure above which overlay network is built. It is the underlying network responsible for the delivery of packets across networks.
- Underlay Protocols: BGP, OSPF, IS-IS, EIGRP
An overlay network is a virtual network that is routed on top of underlay network infrastructure, routing decisions would take place with the help of software.
- Overlay Protocols: VXLAN, NVGRE, GRE, OTV, OMP, mVPN
Overlay networking is a method of using software to create layers of network abstraction that can be used to run multiple separate, discrete virtualized network layers on top of the physical network, often providing new applications or security benefits.
Source: Underlay Network and Overlay Network
Attack Vector
VXLAN is a MAC-over-IP overlay network that inherits both layer 2 and layer 3 attack vectors, so it extends the attack vector of Layer 2 networks.
Traditionally, Layer 2 networks can only be attacked from ‘within’ by rogue endpoints — either:
- by having inappropriate access to a LAN and snooping on traffic,
- by injecting spoofed packets to ‘take over’ another MAC address, or
- by flooding and causing denial of service.
A MAC-over-IP mechanism for delivering Layer 2 traffic significantly extends this attack surface. This can happen by rogues injecting themselves into the network:
- by subscribing to one or more multicast groups that carry broadcast traffic for VXLAN segments and also
- by sourcing MAC-over-UDP frames into the transport network to inject spurious traffic, possibly to hijack MAC addresses.
This document does not incorporate specific measures against such attacks, relying instead on other traditional mechanisms layered on top of IP. This section, instead, sketches out some possible approaches to security in the VXLAN environment.
- Traditional Layer 2 attacks by rogue end points can be mitigated by limiting the management and administrative scope of who deploys and manages VMs/gateways in a VXLAN environment. In addition, such administrative measures may be augmented by schemes like 802.1X for admission control of individual end points. Also, the use of the UDP-based encapsulation of VXLAN enables configuration and use of the 5-tuple-based ACL (Access Control List) functionality in physical switches.
- Tunneled traffic over the IP network can be secured with traditional security mechanisms like IPsec that authenticate and optionally encrypt VXLAN traffic. This will, of course, need to be coupled with an authentication infrastructure for authorized end points to obtain and distribute credentials.
- VXLAN overlay networks are designated and operated over the existing LAN infrastructure. To ensure that VXLAN end points and their VTEPs are authorized on the LAN, it is recommended that a VLAN be designated for VXLAN traffic and the servers/VTEPs send VXLAN traffic over this VLAN to provide a measure of security.
- In addition, VXLAN requires proper mapping of VNIs and VM membership in these overlay networks. It is expected that this mapping be done and communicated to the management entity on the VTEP and the gateways using existing secure methods.
Source: RFC 7348
EAP over LAN
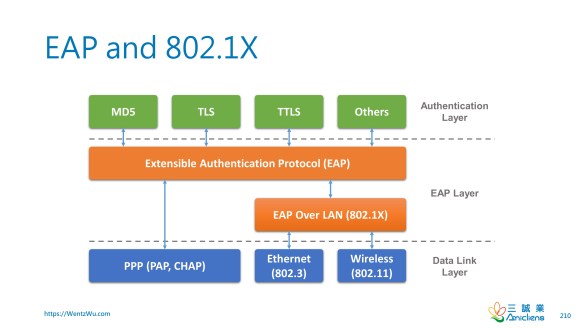
IEEE 802.1X is an IEEE Standard for port-based Network Access Control (PNAC). It is part of the IEEE 802.1 group of networking protocols. It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
IEEE 802.1X defines the encapsulation of the Extensible Authentication Protocol (EAP) over IEEE 802.11, which is known as “EAP over LAN” or EAPOL. EAPOL was originally designed for IEEE 802.3 Ethernet in 802.1X-2001, but was clarified to suit other IEEE 802 LAN technologies such as IEEE 802.11 wireless and Fiber Distributed Data Interface (ANSI X3T9.5/X3T12 and ISO 9314) in 802.1X-2004. The EAPOL was also modified for use with IEEE 802.1AE (“MACsec”) and IEEE 802.1AR (Secure Device Identity, DevID) in 802.1X-2010 to support service identification and optional point to point encryption over the internal LAN segment.
Source: Wikipedia
Reference
- Virtual eXtensible Local Area Network (VXLAN): A Framework for Overlaying Virtualized Layer 2 Networks over Layer 3 Networks (RFC 7348)
- Virtual Extensible LAN (Wikipedia)
- What is VXLAN? (Juniper)
- Underlay Network and Overlay Network
- A Network Engineer’s Perspective of Virtual Extensible LAN (VXLAN)
- What do TOR, EOR and MOR mean?
- Popular ToR and ToR Switch in Data Center Architectures
- VxLAN | Part 1 – How VxLAN Works (YouTube)
- VXLAN Introduction (YouTube)
- Fundamentals of SD-WAN
- Private VLAN
- Virtual Extensible LAN
- RFC 7348: Virtual eXtensible Local Area Network (VXLAN): A Framework for Overlaying Virtualized Layer 2 Networks over Layer 3 Networks
您的公司決定要構建一個虛擬化的數據中心,將提供雲服務作為一項新業務。 預計達到財務收支平衡需要五千名客戶。 以下哪項是支持這個新業務的最佳技術? (Wentz QOTD)
A. Virtual LAN (VLAN)
B. Private VLAN
C. EAP over LAN
D. Virtual eXtensible Local Area Network (VXLAN)

Pingback: 虛擬區域網路擴展(Virtual Extensible LAN:VXLAN) – Choson資安大小事