
Organizations have to ensure the alignment of the security function to business strategy, goals, mission, and objectives. Which of the following statements is least related to the security function? (Wentz QOTD)
A. Employ symmetric cryptographic algorithms to encrypt files.
B. Conduct internal audits to ensure the effectiveness of security controls.
C. Establish a security perimeter to partition nonsecurity functions in a computer system.
D. Assign a person to be in charge of information security and report to senior management.
Kindly be reminded that the suggested answer is for your reference only. It doesn’t matter whether you have the right or wrong answer. What really matters is your reasoning process and justifications.
My suggested answer is B. Conduct internal audits to ensure the effectiveness of security controls.
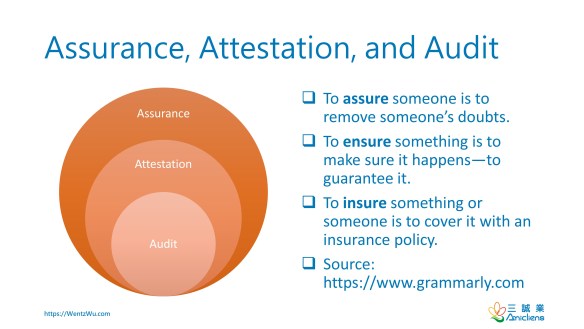
Conducting internal audits to ensure the effectiveness of security controls belongs to the audit function, not the security function.
Security Function
The security function is used in various contexts. From the perspective of governance, it can be implemented as a formal organization unit or executed informally by a person or group.

From the technical point of view, it may refer to cryptographic algorithms or other capabilities provided by the system or a system element to enforce security objectives.

Reference
- Information security assurance for executives
- Reorganising the security function in large organisations
- SC-03 Security Function Isolation
- Fundamental Concepts of IT Security Assurance
- The relationship between internal audit and information security: An exploratory investigation
A BLUEPRINT FOR YOUR SUCCESS IN CISSP
My new book, The Effective CISSP: Security and Risk Management, helps CISSP aspirants build a solid conceptual security model. It is not only a tutorial for information security but also a study guide for the CISSP exam and an informative reference for security professionals.
- It is available on Amazon.
- Readers from countries or regions not supported by Amazon can get your copy from the author’s web site.
組織必須確保安全功能(security function)與業務戰略,目標,任務和目標保持一致。 以下哪項敍述與安全功能最沒有關係?(Wentz QOTD)
A. 採用對稱密碼演算法來加密文件。
B. 進行內部稽核以確保安全控制的有效性。
C. 電腦系統建立安全邊界(security perimeter)以劃分非安全功能。
D. 指派一名負責資訊安全的人員,並向高階主管報告。

Would the security function not be conducting its own audits? How else would it know whether its policies are being followed and effective?