People, processes, and technologies (PPT) are significant components of an information security strategy. An assurance system can remove doubts and render confidence in security to stakeholders. Which of the following is not true?
A. CISSP is accredited per the stringent requirements of ISO 17024
B. CMMI is applicable to procurement in terms of software engineering
C. TCSEC prescribes a computing system shall address covert channels
D. CC assures a product with EAL7 is more secure than one with EAL 4
Kindly be reminded that the suggested answer is for your reference only. It doesn’t matter whether you have the right or wrong answer. What really matters is your reasoning process and justifications.
My suggested answer is D. CC assures a product with EAL7 is more secure than one with EAL 4.
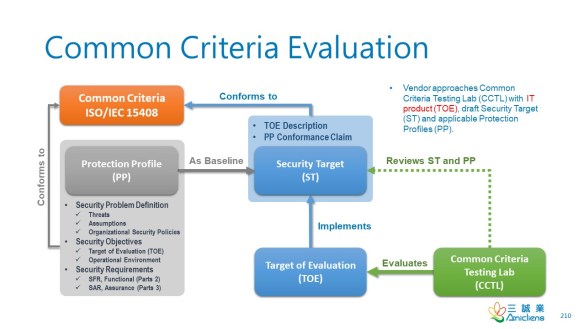
Common Criteria (CC)
The Common Criteria (CC) doesn’t prescribe Security Functional Requirements (SFR) and SAR (Security Assurance Requirement) as TCSEC did. Instead, PP (Protection Profile) and ST (Security Target) are developed to specify SFRs and SARs that are grouped into classes, families, and components.
Protection Profile (PP)
The National Information Assurance Partnership (NIAP) approved 47 Protection Profiles that are categorized into 24 types, such as Application Software, BIOS Update, Certificate Authority, Network Device, Firewall, USB Flash Drive, Web Browser, Wireless LAN, just name a few. So, CC applies to various IT products. Vendors can develop the ST based on PPs and extend them.
Security Target (ST)
In CC, the resolution of covert channels depends on whether the ST includes the covert-channel related SFR, e.g., Information flow control functions (FDP_IFF). For example:
- The Protection Profile for Application Software includes some SFRs in Class FDP: User data protection, but the SFR, FDP_IFF, that deals with covert channels is not covered.
- Given one application software with EAL 1 and the other with EAL 7, if their STs are based on the Protection Profile for Application Software and don’t extend it, then both of them don’t address covert channels.
Evaluation Assurance Level (EAL)
The CC EAL (Evaluation Assurance Level) is not determined by SFR directly. EAL is determined by SAR, the scope, depth, and rigor of the evaluation. The comparison of EALs makes sense only if two products have the same scope of ST developed based on the same set of PPs. A product with higher EAL may not necessarily address the covert channel like one with a lower EAL does, as mentioned above.
In addition to the scope, the depth, and rigor of the evaluation varies. For example, a product vendor seeking EAL1 submits the product (TOE) to the lab. They don’t need to participate in the evaluation. On the contrary, the lab tests the product solely based on the product manual, and the test won’t get inside the internal design. So, EAL1 just means the product works functionally, as the product manual says. However, EAL7 is rigid and deep. It requires and verifies a formal design.
TCSEC
TCSEC prescribes a B2-class system shall address covert channels. The following are the preface of TCSEC:
CISSP
CMMI-ACQ
CMMI® (Capability Maturity Model® Integration) models are collections of best practices that help organizations to improve their processes. These models are developed by product teams with members from industry, government, and the Carnegie Mellon® Software Engineering Institute (SEI). This model, called CMMI for Acquisition (CMMI-ACQ), provides a comprehensive integrated set of guidelines for acquiring products and services.
Reference
人員,流程和技術(PPT)是信息安全策略的重要組成部分。 保證體係可以消除疑慮,並使利益相關者對安全性充滿信心。 以下哪一項是不正確的?
A. CISSP符合ISO 17024的嚴格要求
B. CMMI適用於軟件工程方面的採購
C. TCSEC規定計算系統應處理秘密通道
D. CC確保具有EAL7的產品比具有EAL 4的產品更安全