
You are actively engaging in the open-source community of cryptography and reviewing the source code of a stream cipher to implement on mobile apps. Which of the following is the best justification for selecting the open-source cipher instead of AES? (Source: Wentz QOTD)
A. Shorter key length
B. Lower requirement for hardware capacity
C. Stronger work factor
D. Open design
Kindly be reminded that the suggested answer is for your reference only. It doesn’t matter whether you have the right or wrong answer. What really matters is your reasoning process and justifications.
My suggested answer is B. Lower requirement for hardware capacity.
Compared with block ciphers, stream ciphers typically:
- Execute at a higher speed.
- Have lower hardware requirement
- Can be susceptible to serious security problems if used incorrectly
Key Length
Both stream ciphers and block ciphers are symmetric ciphers, the requirement of key length won’t vary too much. Moreover, shorter key length makes a strem cipher more vulnerable.
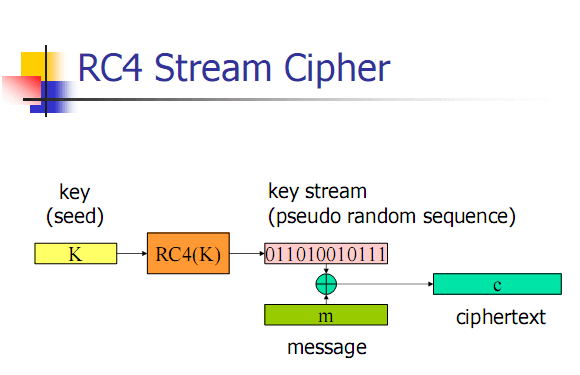
For example, RC4 is a well-known stream cipher. The standard 64-bit WEP uses a 40 bit key with a 24-bit initialization vector (IV) to form the RC4 key, which can be recovered in as little as one minute because of the short key length.
Work Factor
Generally speaking, block ciphers have stronger work factor that stream ciphers under the same conditions. Block ciphers can apply more rounds of complex cryptographic operations. Confusion and diffusion can be applied to block ciphers, but only confusion can be applied to stream ciphers.
Open Design
Both the stream cipher from the open-source community and AES meet the principle of open design.
The principle of open design states that the security of a mechanism should not depend on the secrecy of its design or implementation.
Source: Matt Bishop
Advanced Encryption Standard Process
The Advanced Encryption Standard (AES), the symmetric block cipher ratified as a standard by National Institute of Standards and Technology of the United States (NIST), was chosen using a process lasting from 1997 to 2000 that was markedly more open and transparent than its predecessor, the Data Encryption Standard (DES). This process won praise from the open cryptographic community, and helped to increase confidence in the security of the winning algorithm from those who were suspicious of backdoors in the predecessor, DES.
AES finalists
All five algorithms, commonly referred to as “AES finalists”, were designed by cryptographers considered well-known and respected in the community. The AES2 conference votes were as follows:
- Rijndael: 86 positive, 10 negative
- Serpent: 59 positive, 7 negative
- Twofish: 31 positive, 21 negative
- RC6: 23 positive, 37 negative
- MARS: 13 positive, 84 negative
Selection of the winner
On October 2, 2000, NIST announced that Rijndael had been selected as the proposed AES and started the process of making it the official standard by publishing an announcement in the Federal Register on February 28, 2001 for the draft FIPS to solicit comments. On November 26, 2001, NIST announced that AES was approved as FIPS PUB 197.
NIST won praises from the cryptographic community for the openness and care with which they ran the standards process. Bruce Schneier, one of the authors of the losing Twofish algorithm, wrote after the competition was over that “I have nothing but good things to say about NIST and the AES process.”
Source: Wikipedia
Reference
- Design Principles for Security Mechanisms
- Kerckhoffs’s principle
- Advanced Encryption Standard process
- Stream cipher facts for kids
- How Secure is Secure? On Message and IV Lengths for Synchronous Stream Ciphers
- Stream Cipher vs Block Cipher
- Difference Between Block Cipher and Stream Cipher
- Grain – A Stream Cipher for Constrained Environments
- A survey of lightweight stream ciphers for embedded systems
- Stream cipher
- Block cipher
- Introduction to Modern Cryptography
- Chapter 2 Stream Ciphers
A BLUEPRINT FOR YOUR SUCCESS IN CISSP
My new book, The Effective CISSP: Security and Risk Management, helps CISSP aspirants build a solid conceptual security model. It is not only a tutorial for information security but also a study guide for the CISSP exam and informative reference for security professionals.
- It is available on Amazon.
- Readers from countries or regions not supported by Amazon can get your copy from the author’s web site.
您正在積極參與密碼學的開源社群,並檢視流密碼的原始程式碼以應用在行動裝置的應用程序上。 以下哪項是選擇這個開源加密器,而不是AES的最佳理由?
A. 較短的密鑰長度
B. 較低的硬件容量要求
C. 更高的工作係數
D. 開放式設計

Pingback: Kryptografia - szyfry strumieniowe
Pingback: Cryptography - stream ciphers