
You are implementing remote access solutions to support employees traveling on business. They will connect mobile phones or laptops to corporate networks, on the road or in the hotel, via the unprotected public network. Which of the following is least likely used?
A. 802.1X
B. eXtensible Access Control Markup Language
C. IPSec VPN with tunnel mode
D. RADIUS
Kindly be reminded that the suggested answer is for your reference only. It doesn’t matter whether you have the right or wrong answer. What really matters is your reasoning process and justifications.
My suggested answer is A. 802.1X.
Extensible Authentication Protocol (EAP) messages are encapsulated within:
- PPP
- 802.1X
Point-to-Point Protocol (PPP)
The standard PPP frame structure supports two authentication protocols:
- c023 Password Authentication Protocol (RFC 1134, 1989)
- c223 Challenge Handshake Authentication Protocol (RFC 1131, 1992)
Extensible Authentication Protocol (EAP), as a PPP extension (RFC 2284, 1998), extends authentication mechanisms and improves the insecure PAP and CHAP, while SPAP and MS-CHAP are proprietary improvements.
EAP becomes a standalone authentication protocol since 2004 (RFC 3748).
RADIUS
RADIUS is an authentication framework based on the client/server model which supports multiple authentication mechanisms through EAP.
- RADIUS stands for Remote Authentication Dial-In User Service and was developed to authenticate, authorize, and account (AAA) users.
- RADIUS is a client/server protocol that runs in the application layer and can use either TCP or UDP as transport. RADIUS is often the back-end of choice for 802.1X authentication as well.
- RADIUS protocol can encapsulate EAP messages. It is often used by Network Access Server (NAS) devices to forward EAP packets between IEEE 802.1X endpoints and AAA servers to facilitate IEEE 802.1X.
Source: Wikipedia
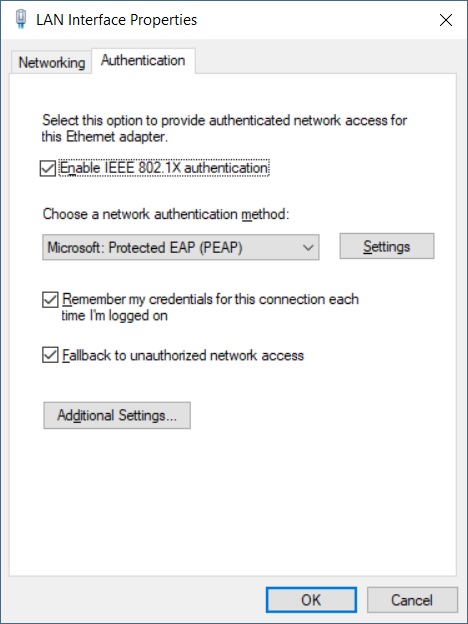
802.1X
IEEE 802.1X enables authenticated access to IEEE 802 media, including Ethernet, Token Ring, and 802.11 wireless LANs. It defines the encapsulation of the Extensible Authentication Protocol (EAP) over IEEE 802, which is known as “EAP over LAN” or EAPOL (Port-based Network Access Control).
(Source: Wikipedia)
There are three basic pieces to 802.1X authentication:
- Supplicant: A software client running on the Wi-Fi workstation.
- Authenticator: The Wi-Fi access point.
- Authentication Server: An authentication database, usually a radius server such as Cisco ACS*, Funk Steel-Belted RADIUS*, or Microsoft IAS*.
Source: Intel
EAP over LAN (Wired)
EAP for Wireless
IPSec
- Tunnel Mode supports routing and NAT-Traversal and encapsulates the source IP payload.
- Transport Mode modifies the original IP packets and typically to support other tunnel protocols, e.g. L2TP.
- AH is used for authentication; ESP for encryption.
XACML
XACML stands for “eXtensible Access Control Markup Language”. The standard defines a declarative fine-grained, attribute-based access control policy language, an architecture, and a processing model describing how to evaluate access requests according to the rules defined in policies.
XACML is primarily an attribute-based access control system (ABAC), where attributes (bits of data) associated with a user or action or resource are inputs into the decision of whether a given user may access a given resource in a particular way.
Source: Wikipedia
For example, VPN access can be authorized based on the following rules or criteria:
- Country equals to Taiwan,
- Department is Sales,
- Seniority is greater than 1 year, and
- Connection time is during the office hour
Summary
- 802.1X is used to encapsulate EAP messages over LAN (802.3 or 802.11), not VPN.
- The VPN authentication can be completed using EAP without 802.1X (EAP Over LAN).
References
- RFC 3748: Extensible Authentication Protocol (EAP), 2004
- RFC 3579: RADIUS Support For Extensible Authentication Protocol (EAP), 2003
- RFC 2865: Remote Authentication Dial In User Service (RADIUS), 2000
- RFC 1661: The Point-to-Point Protocol (PPP), 1994
- RFC 1548: The Point-to-Point Protocol (PPP), 1993
- RFC 1331: The Point-to-Point Protocol (PPP) for the Transmission of Multi-protocol Datagrams over Point-to-Point Links, 1992
- RFC 1171: The Point-to-Point Protocol for the Transmission of Multi-Protocol Datagrams Over Point-to-Point Links, 1990
- RFC 1134: The Point-to-Point Protocol: A Proposal for Multi-Protocol Transmission of Datagrams Over Point-to-Point Links, 1989




I am looking to get ready for CISSP ( ISSAP, ISSEP, ISSMP)PRACTICE QUESTIONS…. Please help….thank you