
You registered a new user account, activated through confirming a short message sent to your mobile phone on a website. Whenever you are signing in, the website will send an authentication code to your mobile phone after receiving the username and password and verify your response to complete the sign-in process. Which of the following best describes the authentication mechanism?
A. Zero-knowledge proof
B. One-factor authentication
C. Two-factor authentication
D. Challenge-Handshake Authentication Protocol (CHAP)
Kindly be reminded that the suggested answer is for your reference only. It doesn’t matter whether you have the right or wrong answer. What really matters is your reasoning process and justifications.
My suggested answer is C. Two-factor authentication.
Some instructors or security professionals regard the authentication in question is the one-factor authentication, something-you-know, because the mobile authentication code is “known” to the subject. However, it’s not the case in my view as the mobile authentication code, according to based on the NIST SP 800 63-3, is used to verify if the subject possesses and controls the mobile phone pre-registered with the CSP, something-you-have.
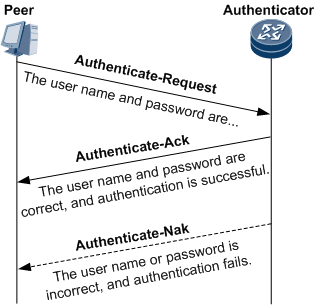
Challenge-Handshake Authentication Protocol (CHAP)
The mobile authentication code works like the mechanism, challenge/response, but it’s not the authentication protocol, Challenge-Handshake Authentication Protocol (CHAP), which uses one-way function and follows specific packet formate defined in RFC 1994.
Authentication Factor and Authenticator

The classic paradigm for authentication systems identifies three factors as the cornerstones of authentication:
• Something you know (e.g., a password).
• Something you have (e.g., an ID badge or a cryptographic key).
• Something you are (e.g., a fingerprint or other biometric data).MFA refers to the use of more than one of the above factors. The strength of authentication
systems is largely determined by the number of factors incorporated by the system — the more factors employed, the more robust the authentication system.In digital authentication the claimant possesses and controls one or more authenticators that have been registered with the CSP and are used to prove the claimant’s identity.
A digital authentication system may incorporate multiple factors in one of two ways:
1. The system may be implemented so that multiple factors are presented to the verifier; or
2. Some factors may be used to protect a secret that will be presented to the verifier.Source: NIST SP 800 63-3
Reference
- Challenge-Handshake Authentication Protocol
- RFC 1994 (CHAP)
- ME60 V800R010C10SPC500 Feature Description – User Access 01
A BLUEPRINT FOR YOUR SUCCESS IN CISSP
My new book, The Effective CISSP: Security and Risk Management, helps CISSP aspirants build a solid conceptual security model. It is not only a tutorial for information security but also a study guide for the CISSP exam and an informative reference for security professionals.
- It is available on Amazon.
- Readers from countries or regions not supported by Amazon can get your copy from the author’s web site.
您在一個網站註冊了新的使用者帳戶,該帳戶是通過在網站上確認發送到您的手機的短信來啟用的。 每次登入在送出使用者名稱和密碼後,網站都會將驗證碼發送給您的手機,您必須將驗證碼輸入到網站後才能完成登錄。 以下哪項最能描述這樣的身份驗證機制?
A. 零知識證明 (Zero-knowledge proof)
B. 單因子認證 (One-factor)
C. 雙因子認證 (Two-factor)
D. 挑戰交握身份驗證協議 (CHAP)
